Online Md5 Generator
About Online Md5 Generator
MD5, also known as Message Digest algorithm 5, is a cryptographic hash function made of a 128-bit algorithm. Its primary function is to create a unique digital fingerprint for data to detect any changes made to it.
The process is done for a file or a password; hence it is used for password hashing and data encryption. This makes it easy to know whether data has been corrupted. It takes input data and generates a hash value of a fixed length.
MD5 users can use this hash value from a particular data source and compare it to the MD5 of the file's destination. For example, we generate a hash from a specific website like seotoolsaudit.com before sending a file.
On receiving the file, the receiving end also generates a hash for the same file from the same online MD5 Generator. If the string is unaltered, this is verification that the file has not been tampered with. Even the slightest difference is evidence of corruption.
Though MD5 is a unique fingerprint, it is crucial to note that it is not a form of encryption but one-way and irreversible.
What is the function of our MD5 Generators?
MD5 generators create a unique hash value for a particular string or text. The SEO Tools Audit MD5 generator does that in a few seconds for any given entry at no cost. All you need to do is enter the data you wish to convert, and our robust algorithm will develop a unique 32-character hexadecimal alphanumeric string.
Features and Benefits of Online MD5 Generator
Here at SEO Tools Audit, we pride ourselves on producing unique SEO tools that are easy to use. Our online MD5 Generator falls into that category.
For this tool, all you have to do is enter the text you want an MD5 for, and our algorithm will produce one for you in a matter of seconds. The reply to your request is a tabular form to make it easy to retrieve.
The unique signature we provide you with can be used for various purposes, such as: verifying the integrity of a file, password authentication, and data encryption of sensitive files. In addition, given that it is unique, it serves as a form of security.
It is also quite efficient since an online MD5 generator can produce a hash for large volumes of data. Moreover, the Generator is accessible in a place with an internet connection and has a user-friendly interface to ensure every person's experience is pleasant.
How to use SEO Tools Audit’s Online MD5 Generator?
SEO Tool Audit's tools are straightforward, and the online MD5 Generator is no different. Its operation involves only three steps. These are:
- Go to our page at https://seotoolsaudit.com/online-md5-generator
- Enter the text you need an MD5 for in the provided text box
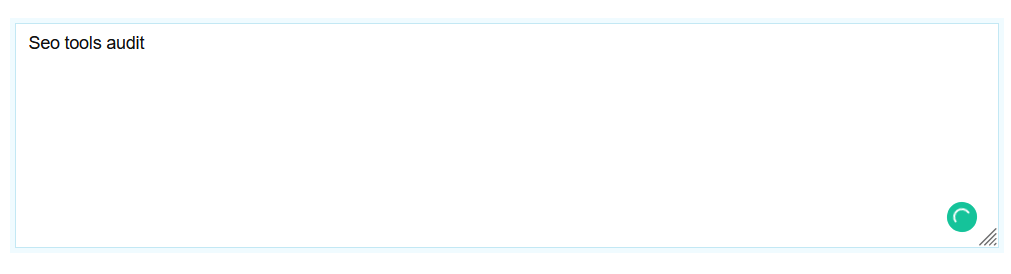
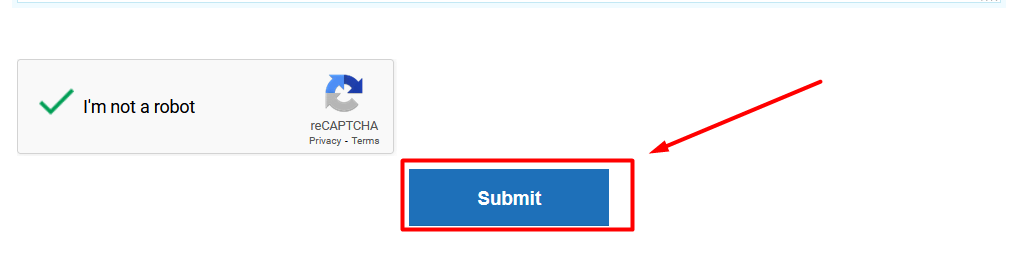
- Click on the blue “Submit” button below the text box
Within a few seconds, our excellent tool will provide a 32-character alphanumeric string for your text. The results are tabular, with the first row containing the given text and the second row containing the MD5 hash.

We highly value your privacy, so no information entered in the text box is retained and not viewed by anyone other than the user. This prevents information theft and protects the privacy of all our users. In addition, we understand the importance of using a reputable and secure generator to protect your information from any security risks, so we ensure what we offer is the best in the market.
FAQs
How safe is MD5?
MD5 is considered safe, but it is susceptible to some things. These include collision attacks and attempts to extend the length. Collision attacks occur when two different messages have the same 32-character hexadecimal code. This compromises the security of the information.
Some attacks also increase the length of the message without necessarily knowing the hash value or the original message.
How likely are collisions to happen with MD5?
Generally, it is quite likely to produce a collision. However, for that to happen, there must be around 6 million files per second being hashed for a period of a hundred years for it to occur. These are high odds, so it is a considerably safe method. However, it is much easier to do it deliberately. More information on this subject can be found in the "Birthday Paradox."
What is the whole point behind rainbow tables?
Rainbow tables are pre-calculated lookup tables that reverse cryptographic hash functions such as MD5. They are used to derive hash values for a large number of plaintexts. They are primarily used in password cracking but have some limitations. For example, they cannot work against "salted" passwords, which means a random value is added to the password before hashing.
For passwords that have not been "salted," a hacker can easily access the password by accessing the hash value and deciphering it with rainbow tables.
Why is MD5 irreversible?
The process of creating the hash is similar to blending ingredients. However, you cannot go back to the original content. This is important for security purposes. For example, if someone gets hold of a hash containing sensitive information, it would not be easy to revert to the original text.
What is the size of an MD5 hash value?
It is typically a 128-bit string. It contains 32 hexadecimal digits, which are digits ranging from 0-9 and A-F.
What is the difference between an MD5 hash and an SHA-256 hash?
One of the defining differences between them is the number of hexadecimal digits produced in the hash. MD5 has 32 digits, while SHA-256 has 64 digits, making it harder to crack and more secure. The input process is also different. MD5 uses the Message Digest process, while SHA-256 uses a more complex process known as the "Secure Hash Algorithm."
LATEST BLOGS
Search
-
Popular Seo Tools
- Plagiarism Checker
- Paraphrasing Tool
- Keyword Position Checker
- Grammar Checker
- Domain Authority Checker
- PageSpeed Insights Checker
- Image Compression Tool
- Reverse Image Search
- Page Authority checker
- Text To Speech
- Backlink Checker
- Backlink Maker
- Domain Age Checker
- Website Ping Tool
- Website Reviewer
- Keyword Density Checker
- Page Size Checker
- Word Counter
- Mozrank Checker
